InfoBeyond
Who We Are?
We are InfoBeyond ...
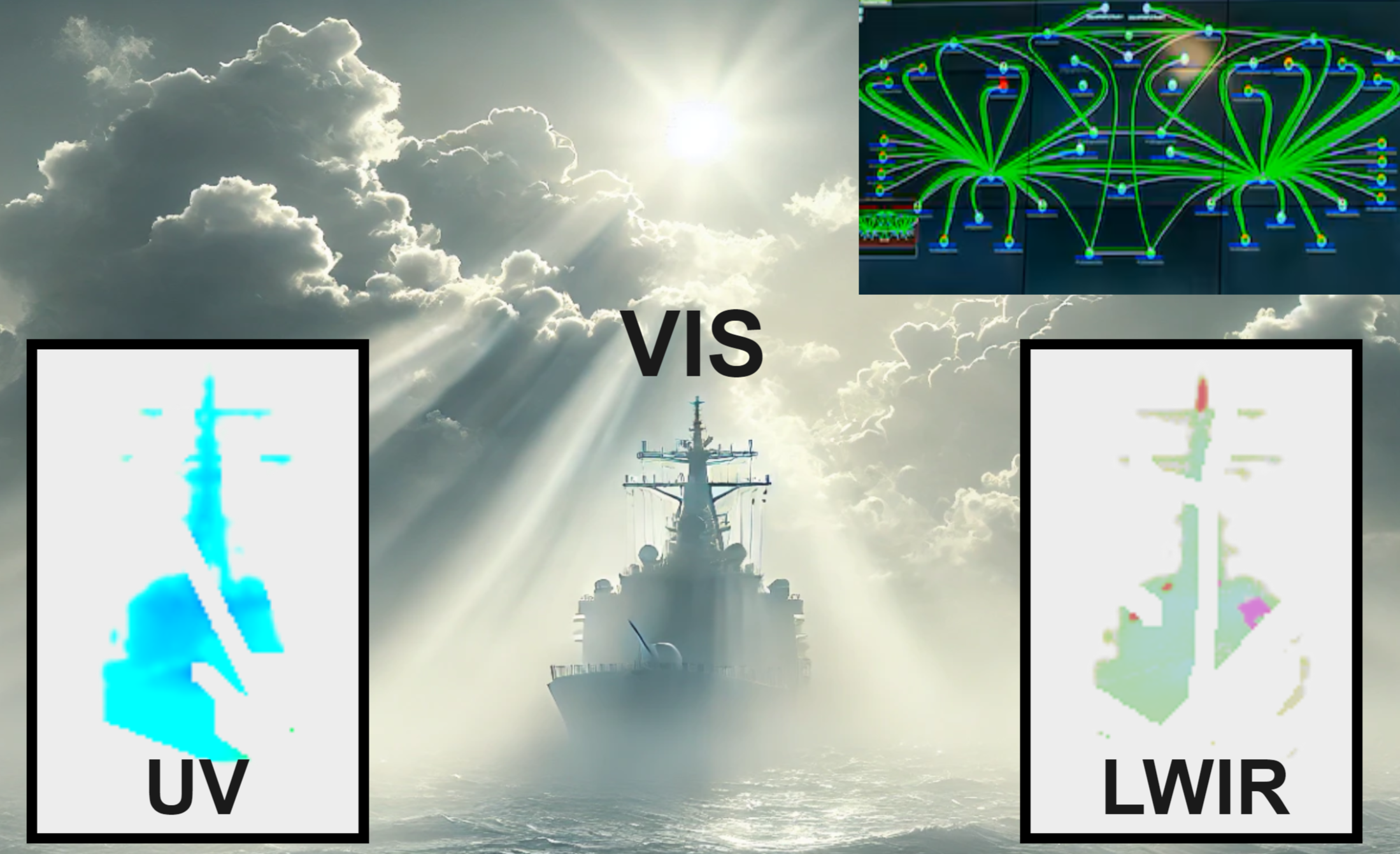
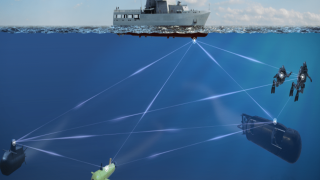
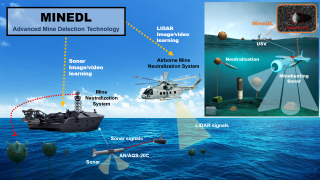
We specialize in delivering groundbreaking technologies in the areas of Cybersecurity, AI, Computer Vision, and Communications for National Defense and Civilian Industries. We wield our passion for innovation to provide key enhancements to businesses and organizations around the globe.
Our Clients
Trusted by Companies, Government Organizations, and Non-Profits Around the World
Our Products
Product Offerings and Solutions
RMF Tool: Streamlining Risk Management Framework Compliance
Are you developing an information system that needs to meet FISMA, NIST, or other federal security standards? Do you want to assess and document compliance with these frameworks efficiently? RMF Tool is designed to simplify this process.
RMF Tool is a compliance automation solution that helps governments, contractors, consultants, and private organizations navigate the NIST Risk Management Framework (RMF). By leveraging NIST SP 800-53, it streamlines key RMF steps, including system categorization, security control selection, and SSP generation, ensuring systems align with the necessary security and privacy controls.
With automated workflows and structured templates, RMF Tool reduces the complexity of compliance, helping organizations save time, improve accuracy, and ensure regulatory alignment without the burden of manual documentation.
Ensure your RMF CompliancePreworkscreen
Preworkscreen is an online COVID-19 self-assessment tool that allows employees to perform self-health checks, log their results, and report to their company's HR/Safety Officers from their mobile phones. It is now available to screen guests and visitors for COVID-19 symptoms before or as they enter the building. It's the state-of-the-art way to protect your employees' safety & health and prevent the spread of Coronavirus throughout your work place. Moreover, it complies with employee self-screening guidelines defined by all U.S. states and Canadian provinces, reduces your company's liability risks, and keeps you up-to-date about your staff's health status in real-time.
Streamline Your Employee ScreeningSecurity Policy Tool
Are you familiar with the access control faults (e.g., Privilege leakage) commonly hidden within access control policies that are identified by NIST ( SP 800-192 )? These faults, if left unfound, create the perfect conditions for data breach, identity theft, and insider attack, e.g., Snowden NSA Leak. Security Policy Tool enables you to easily identify and correct these access control errors before they cause damage to your organization. Help protect your company’s and customer’s data from cyber threats:create, edit, model, test, and verify your access control policies with Security Policy Tool.
Test your Access Control PolicyVehChain: No Hardware-Added Software Tool Offering DoD Intra-Vehicle Security
Future vehicles operate in a more complicated and hostile network environment where cybersecurity cannot be ignored in support of mission operations and command controls. Due to the inherent nature of CAN Bus, all ECUs in a vehicle network communicate without encryption and authentication, resulting in critical security vulnerabilities. VehChain, a Blockchain-reminiscent cryptographic software tool, protects real-time safety-critical vehicle ECUs, networks, commands, and payload data from unintended or unauthorized access, modification, or destruction.
Secure your Vehicle CAN BusSafeCBM
Systems in power plants suffer from gradual deterioration due environmental factors, operational stresses, and aging effects. This calls for advanced power plant Prognostics and Health Management (PHM) technology to achieve sustainable electricity generation and supply in a safe and economic way. To fill this gap, InfoBeyond proposes SafeCBM to provide cost-effective Predictive Maintenance capability subject to strict safety and reliability constraints of energy power plants. SafeCBM enables condition-based monitoring with dynamic-scheduled inspection for power plant components. SafeCBM provides a comprehensive solution for Condition-Based Maintenance (CBM) to increase equipment reliability and reduce maintenance costs in nuclear, solar, wind, coal, and hydrogen power plants.
Optimize your Equipment Monitoring